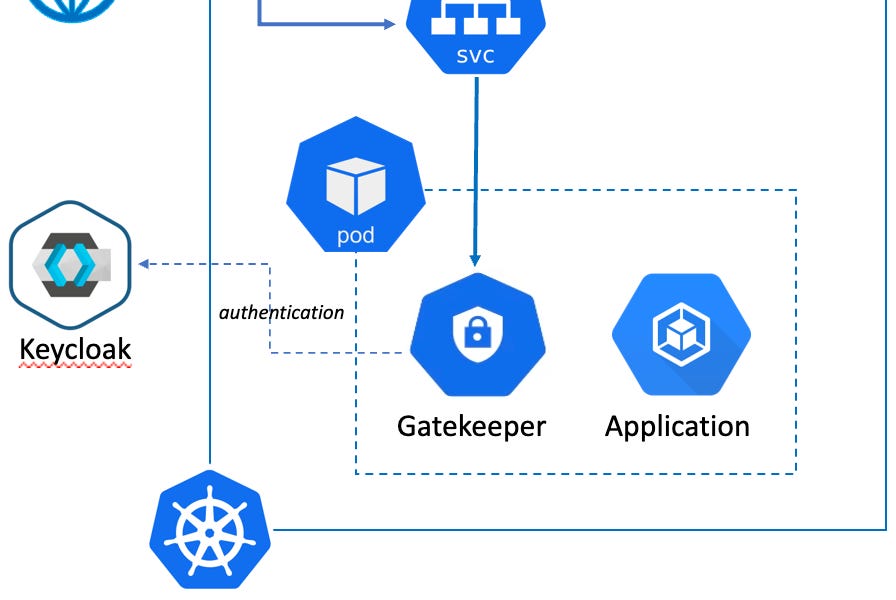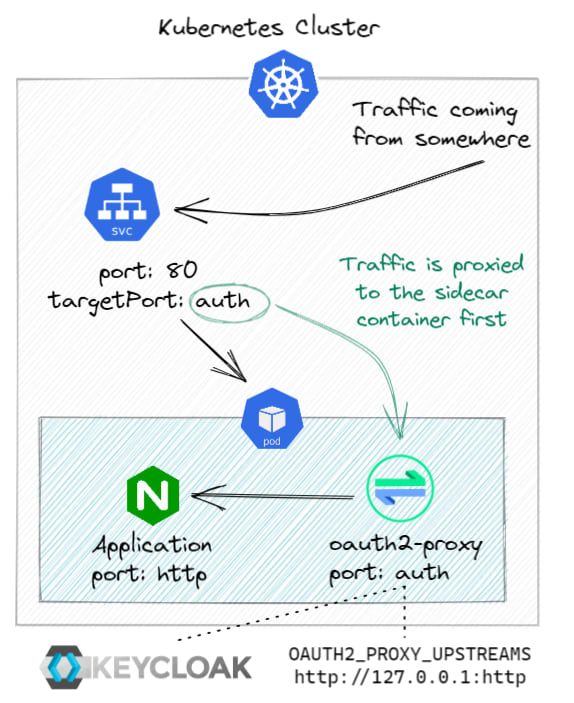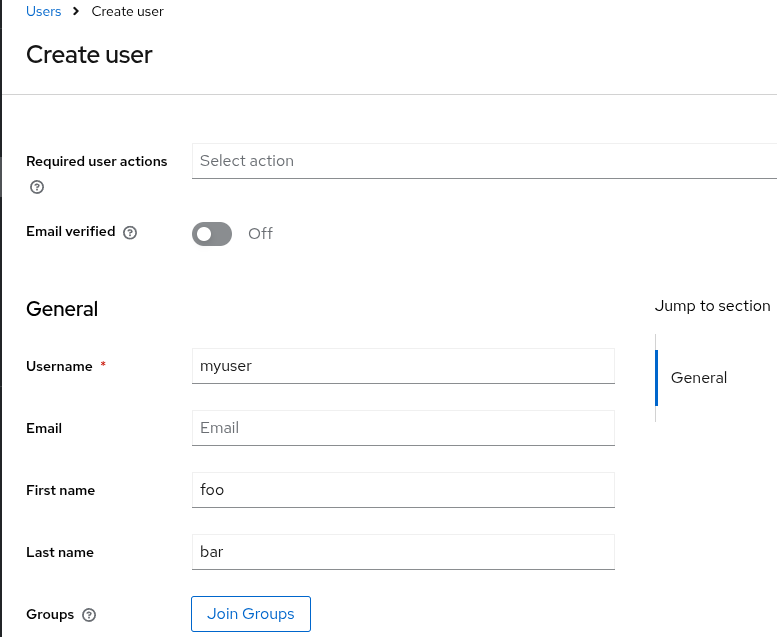
How to protect the Kuberentes dashboard using keycloak oidc and oauth2-proxy - Middleware|Technologies
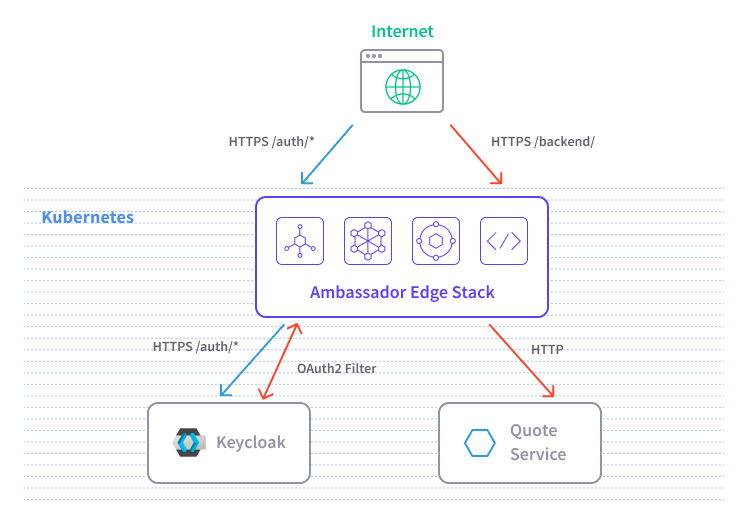
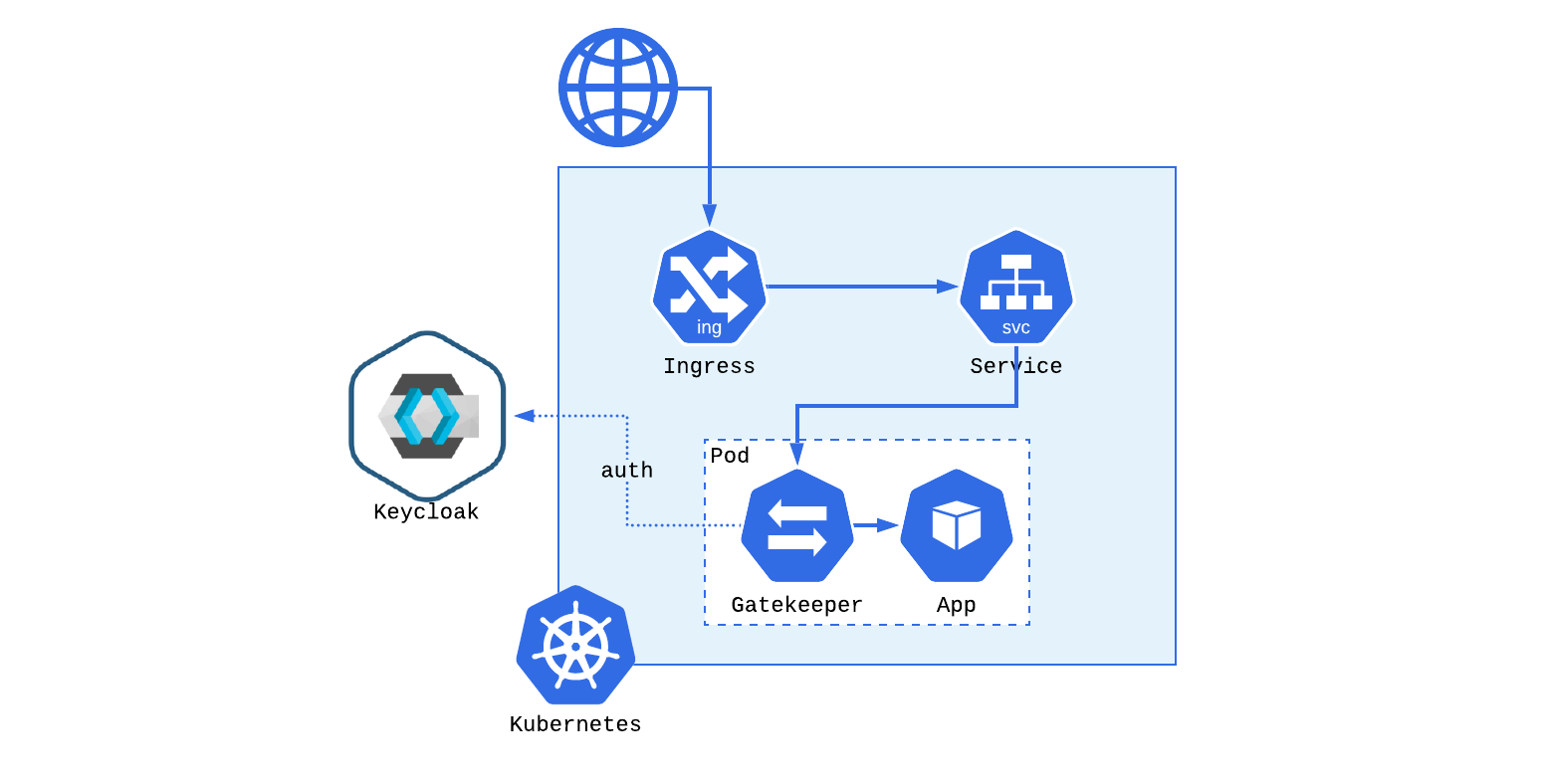
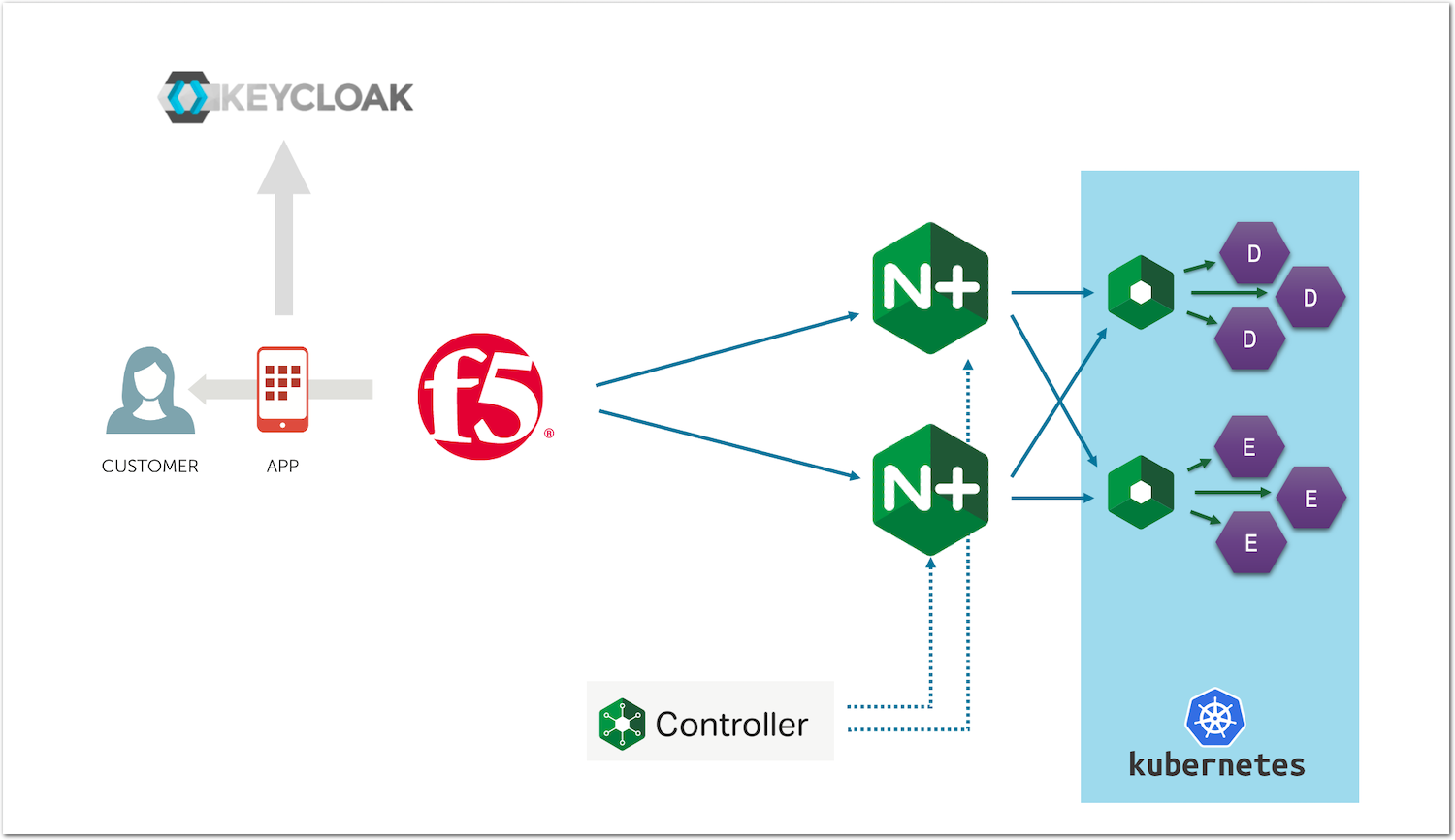
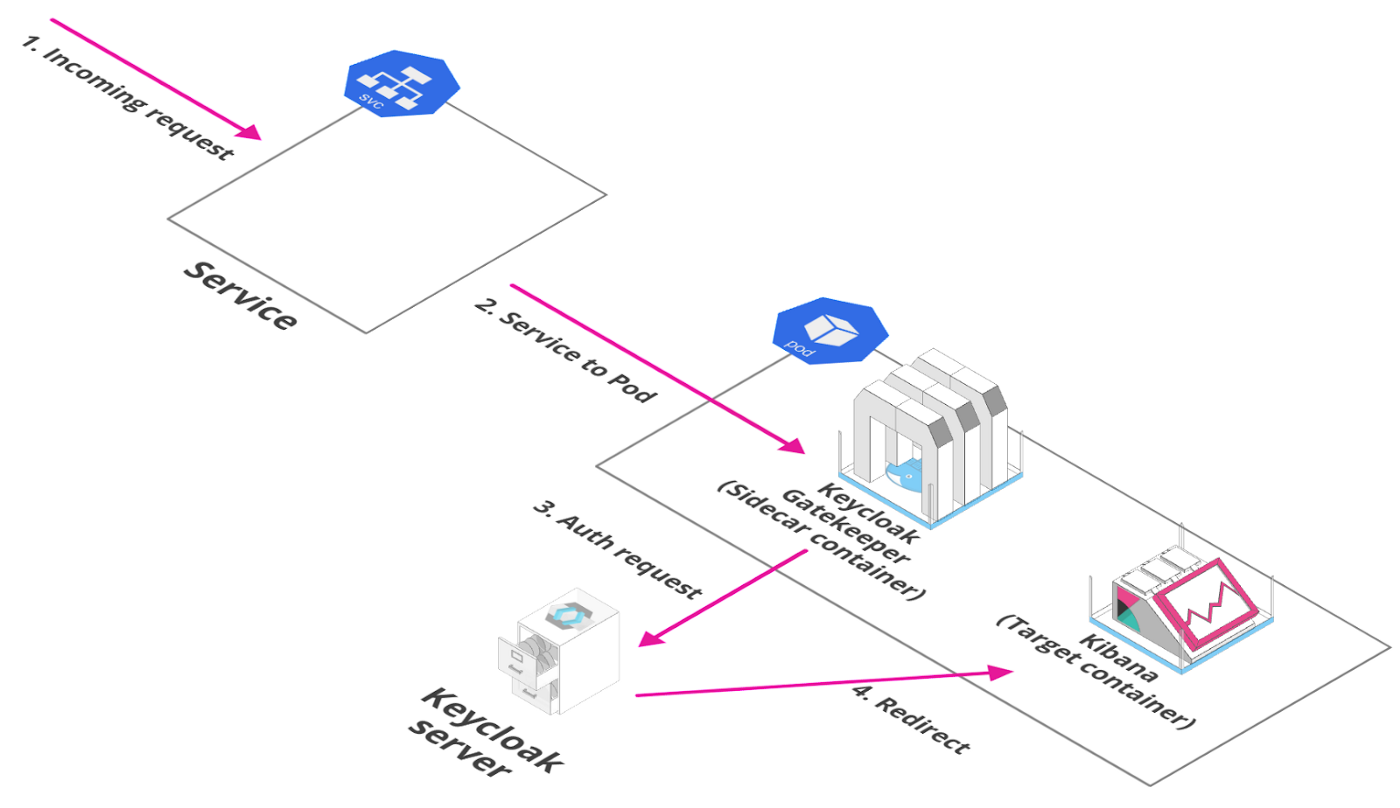
Step-by-Step Centralized Authentication for Kubernetes with Keycloak and the Ambassador Edge Stack | by Alex Gervais | Ambassador Labs
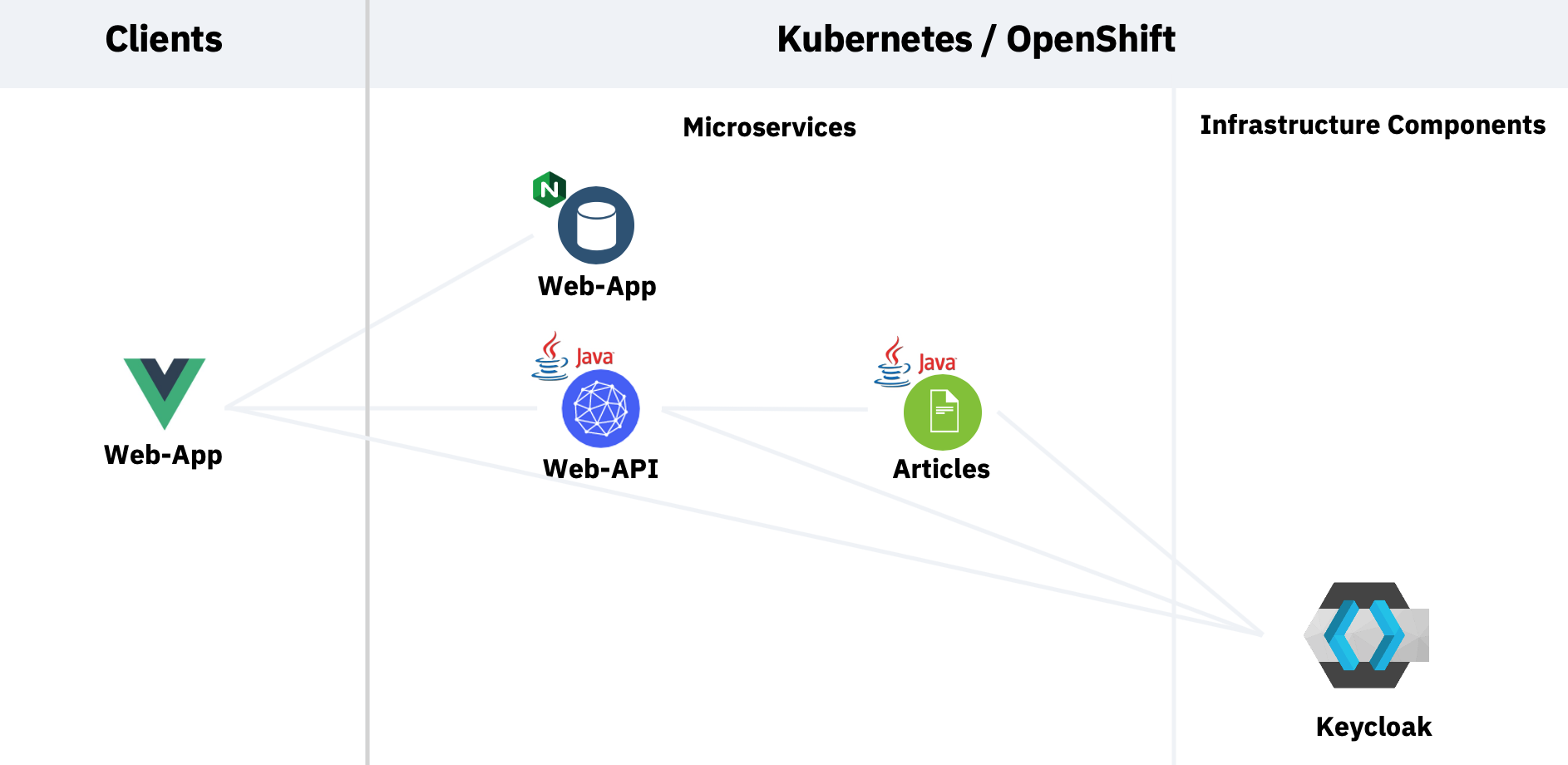
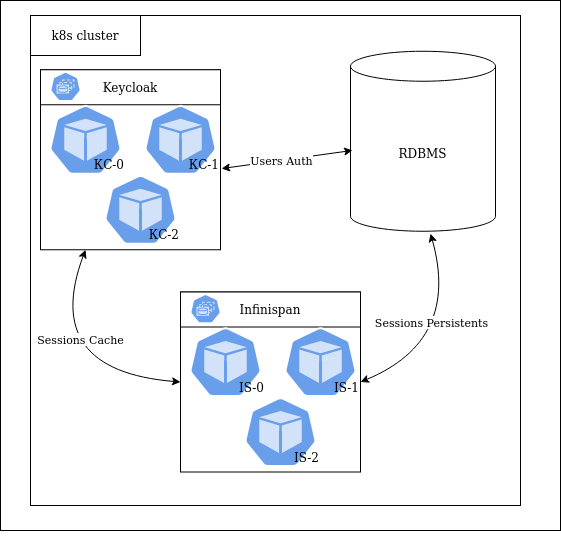
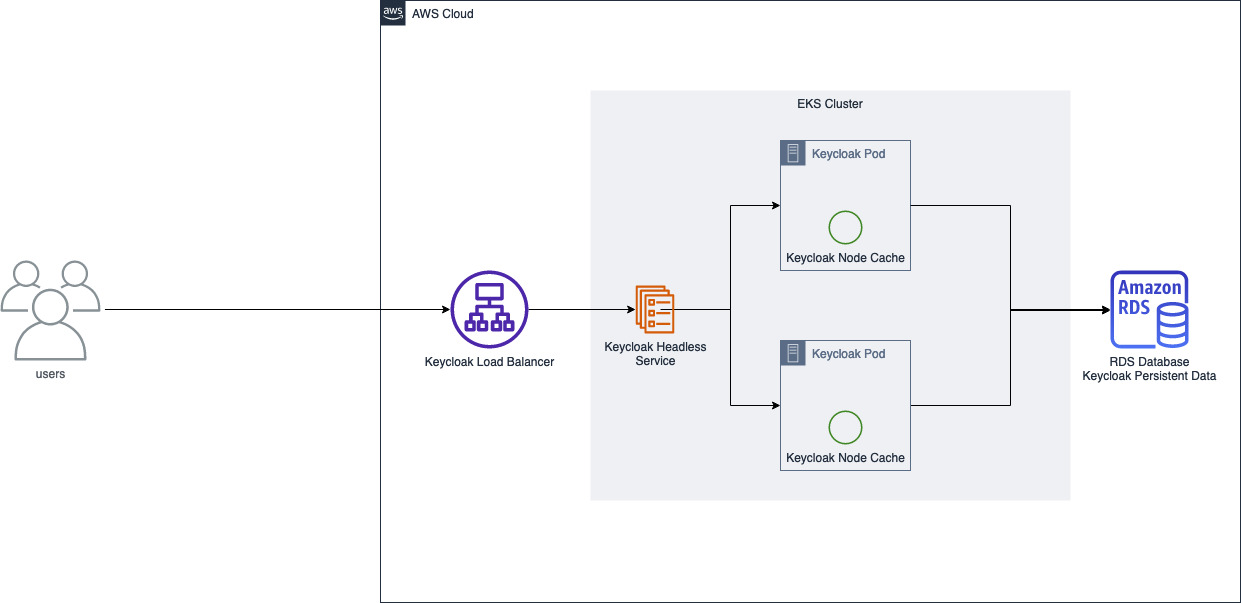
Running Multiple Replicas of Keycloak on a Kubernetes Cloud | by Sitikantha Sarangi | Prodevans-Keycloak | Medium